20 Great Pieces Of Advice For Picking Messenger Sites
Wiki Article
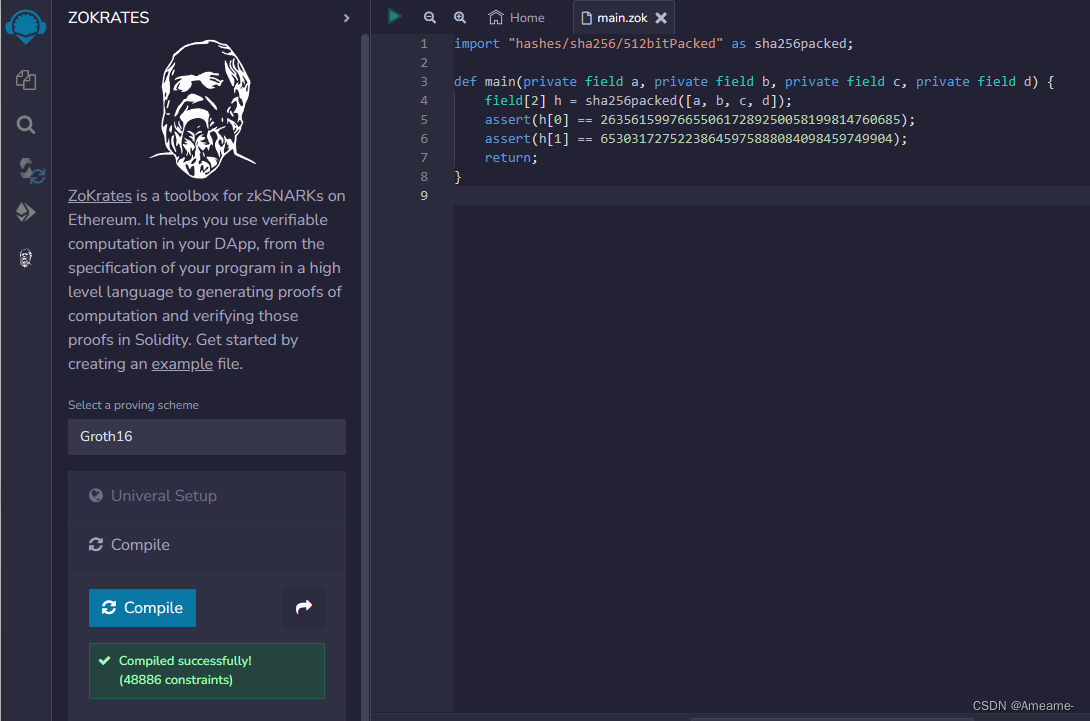
"The Shield Powered By Zk" What Zk-Snarks Can Hide Your Ip Address And Personal Information From The Public
In the past, privacy applications have operated on a model of "hiding from the eyes of others." VPNs direct users to another server, and Tor is able to bounce you around different nodes. While they are useful, they basically hide your source of information by moving it but not proving it isn't required to be disclosed. Zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) introduce a radically different method of reasoning: you can establish that you're authorized in performing an action without disclosing the entity it is that you're. It is possible to prove this in Z-Text. you can broadcast a message that is sent to BitcoinZ blockchain. The network will confirm you're legitimately a participant and have an active shielded identity, however, it is not able to determine the specific address you sent it to. Your address, your name is not known, and the existence of you in the chat becomes inaccessible by the observing party, and is deemed to be valid by the protocol.
1. Dissolution of Sender-Recipient Link
Traditional messaging, even with encryption, reveal the relationship. Anyone who is watching can discern "Alice is speaking to Bob." ZK-SNARKs destroy this connection completely. When Z-Text releases a shielded transactions and the zk-proof is a confirmation that there is a valid transaction--that's right, the sender's balance is sufficient and keys that are correct, but does not divulge who the sender is or recipient's address. To anyone who is not a part of the network, the transaction will appear as a sound wave that originates through the system itself, however, it's not coming from any particular person. It is when the connection between two individuals is computationally impossible to establish.
2. IP address protection at the Protocol Level, but not at the App Level
VPNs and Tor can protect your IP by routing traffic through intermediaries, but those intermediaries also become new points of trust. Z-Text's implementation of zk_SNARKs is a guarantee that it is in no way relevant to verification of the transaction. When you transmit your private message through the BitcoinZ peer-to-peer network, it means you can be one of thousands of nodes. The zk-proof assures that even observers observe the Internet traffic, they're unable to identify the packet of messages that are received and the wallet or account that originated it, because the confirmation doesn't include the information. This makes the IP irrelevant.
3. The Abolition of the "Viewing Key" Difficulty
In a variety of blockchain privacy platforms, you have the option of having a "viewing key" with the ability to encrypt transaction details. Zk-SNARKs, which are part of Zcash's Sapling protocol which is employed by Ztext can allow you to disclose your information in a selective manner. One can show the message you left without revealing your IP, any of your other transactions, or even the whole content of the message. This proof is only to be disclosed. A granular control of this kind is impossible when using IP-based networks where sharing messages automatically reveal the source address.
4. Mathematical Anonymity Sets That Scale Globally
When you are using a mixing or VPN you are restrained to only the other people of that particular pool at the moment. Through zkSARKs's zk-SNARKs service, your anonym secured is each shielded address throughout the BitcoinZ blockchain. Since the proof proves that the sender has *some* shielded account among millions, but provides no details about the particular one, your protection is shared across the entire network. Your identity is not hidden in a small room of peers, but in a global community of cryptographic identifications.
5. Resistance to Traffic Analysis and Timing Attacks
Advanced adversaries don't only read IPs, they look at how traffic flows. They investigate who's sending data when, and correlate events. Z-Text's use and implementation of zkSARKs in conjunction with a blockchain-based mempool, permits the separation of actions from broadcast. A proof can be constructed offline and broadcast it later while a network node is able to broadcast it. Time stamps of proof's presence in a bloc is not necessarily correlated with the when you first constructed the proof, restricting timing analysis, which often defeats simpler anonymity tools.
6. Quantum Resistance Utilizing Hidden Keys
IP addresses can't be considered quantum-resistant; if an adversary can monitor your internet traffic and, later, break encryption that they have, they are able to link your IP address to them. Zk - SNARKs, like those used in Z-Text protect your keys themselves. The key that you share with the world is never visible on blockchains since the evidence proves that you're holding the correct keys but without revealing it. Quantum computers, later on, could be able to see the proof only, which is not the real key. The information you have shared with us in the past is private as the password used to be used to sign them was never revealed to be hacked.
7. The unlinkable identity of multiple conversations
With a single wallet seed will allow you to make multiple secured addresses. Zk SNARKs will allow you to prove that you're the owner of these addresses without disclosing which one. That means that you could have to have ten conversations with ten different individuals. No observer--not even the blockchain itself--can relate those conversations to same wallet seed. The social graph of your network has been designed to be mathematically unorganized.
8. Elimination of Metadata as a security feature
Spy and regulatory officials often tell regulators "we don't really need the information only the metadata." DNS addresses can be considered metadata. Your conversations with whom you are metadata. Zk SNARKs are distinct among privacy options because they block metadata on a cryptographic level. Transactions themselves are not populated with "from" and "to" fields in plaintext. There's no metadata for submit to. Only the documentation, which does not reveal a specific act took place, not who.
9. Trustless Broadcasting Through the P2P Network
When you connect to the VPN then you can trust the VPN provider to not log. If you're using Tor and trust it to the exit node's ability to not trace you. By using Z-Text, you transmit your zk-proof transaction to the BitcoinZ peer-to'peer network. Then, you connect to some random nodes, transmit an email, and then leave. This is because there's no evidence. They cannot even be certain you are the originator, considering you could be sharing information for someone else. The internet becomes a trustworthy host of sensitive information.
10. "The Philosophical Leap: Privacy Without Obfuscation
Finally, zk-SNARKs represent some kind of philosophical leap, over "hiding" for "proving but not disclosing." Obfuscation techniques recognize that the truth (your ID, IP) is of a high risk and needs be concealed. Zk SNARKs agree that the truth is irrelevant. Only the protocol needs to acknowledge that you're authorized. The change from reactive disguise to active inevitability is one of the fundamental components of the ZK security shield. Your identity and IP address are not concealed. They are essential to the functions of the network and thus are not required as a result of transmission, disclosure, or even request. Have a look at the best zk-snarks for more advice including encrypted text app, encrypted text app, encrypted text, message of the text, private text message, private message app, encrypted app, message of the text, messenger to download, private message app and more.

Quantum-Proofing Your Chats: Why Z-Addresses And Zk-Proofs Resist Future Cryptography
Quantum computing is usually discussed in terms of abstract concepts, a possible boogeyman to break all encryption. But the reality is specific and crucial. Shor's program, if used with a sufficient quantum computer, might theoretically break the elliptic-curve cryptography that makes up the bulk of the internet and cryptographic systems today. The reality is that not all encryption methods are equally vulnerable. Z-Text's design, based on Zcash's Sapling protocol and zk-SNARKs, incorporates inherent properties that thwart quantum decryption in ways that conventional encryption is not able to. The secret lies in what is exposed versus what is obscured. With Z-Text, you can ensure that your public keys are not revealed on your blockchain Z-Text makes sure there's no place for quantum computers in order to sabotage. All of your conversations in the past, as well as your identification, and even your wallet remain sealed, not by complexity alone, but through mathematical invisibility.
1. The Fundamental Risk: Explicit Public Keys
In order to understand the reasons Z-Text is quantum-resistant first learn why other systems are not. As with traditional blockchain transactions your public key gets exposed at the time you purchase funds. A quantum computer is able to take the publicly exposed key and utilize Shor's algorithm obtain your private key. Z-Text's encrypted transactions, utilizing zi-addresses never divulge the public key. The zk-SNARK certifies that you own this key without having to reveal it. The public key is concealed, giving the quantum computer nothing.
2. Zero-Knowledge Proofs as Information Minimalism
Zk-SNARKs are quantum-resistant in that they depend on the complexity of those problems that aren't too easily resolved by quantum algorithms as factoring nor discrete logarithms. Additionally, the proof itself is completely devoid of information on the witnesses (your private password). However, even if quantum computers could possibly break any of the fundamental assumptions underlying the proof it's got nothing to use. This proof is an unreliable cryptographic proof that proves the validity of a sentence without actually containing the truth of the assertion.
3. Shielded addresses (z-addresses) as an Obfuscated Existence
A z-address from the Zcash protocol (used by Z-Text) will never be recorded onto the Blockchain in a manner in which it is linked to a transaction. If you are able to receive money or messages from Z-Text, the blockchain records that a shielded pool transaction has occurred. Your personal address is hidden among the merkle-like tree of notes. Quantum computers scanning the blockchain can only see trees and evidences, not leaves or keys. Your cryptographic address is there, but it's not observed, rendering it inaccessible to retrospective analysis.
4. The "Harvest Now, Decrypt Later" Defense
One of the greatest threats to quantum technology today is not a direct attack that is passively collected. The adversaries can take encrypted data through the internet, then save in a secure location, patiently waiting for quantum computers to develop. With Z-Text, an adversary can scan the blockchain to collect every shielded transaction. However, without viewing keys in the first place, and with no access to the public keys, they are left with none to decrypt. They collect one of the zero-knowledge proofs designed to will not have encrypted messages which they might later decrypt. The message does not have encryption in the proof; the proof is the message.
5. How Important is One-Time Use of Keys
In many cryptographic system, the reuse of a key results in more information that is available for analysis. Z-Text is based upon the BitcoinZ blockchain's application of Sapling it encourages the implementation of diversified addresses. Each transaction has an illegitimate, unique address stemming from the identical seed. This is because even there is a chance that one address could be damaged (by quantum means), the others remain as secure. Quantum resistance can be increased due to the rotational constant of keys this limits the strength for any one key cracked.
6. Post-Quantum Logic in zk SNARKs
Modern zk-SNARKs rely heavily on pairs of elliptic curves that are theoretically insecure to quantum computers. However, the construction of Zcash and Z-Text can be used to migrate. It is intended in order to allow post-quantum secure Zk-SNARKs. Since the keys are not revealed, a switch to a brand new proving system could be accomplished via the protocol itself without needing the users to release their previous history. The shielded pool architecture is capable of being forward-compatible with quantum resistant cryptography.
7. Wallet Seeds and the BIP-39 Standard
Your wallet's seed (the 24 characters) doesn't have to be quantum-secure as. The seed is essentially a high-frequency random number. Quantum computers aren't much greater at brute forcibly calculating 256-bit numbers compared to classical computers due to the limitation of Grover's algorithm. It is the creation of public keys from that seed. The public keys are kept from being discovered by using zk_SNARKs, the seed remains secure even when it is in a post-quantum era.
8. Quantum-Decrypted Metadata vs. Shielded Metadata
Even if quantum computer eventually crack some parts of encryption They still confront problems with Z-Text's ability to hide metadata in the protocol. In the future, a quantum computer might inform you that a particular transaction occurred between two entities if it had their public keys. But if those public keys never were revealed and the transaction is a zero-knowledge proof that doesn't contain information about the address, then the quantum computer only knows the fact that "something happened in the shielded pool." The social graphs, the timing along with the frequency, are largely unnoticed.
9. The Merkle Tree as a Time Capsule
Z-Text stores the messages stored in the blockchain's Merkle Tree of the notes shielded. This structure is inherently resistant from quantum decryption, because it is difficult to pinpoint a specific note requires knowing its dedication to a note as well as the location in the tree. Without a key for viewing, a quantum computer cannot distinguish your note from millions of notes that are in the tree. The time and effort needed to go through all the trees to locate an individual note is massively large, even for quantum computers. The difficulty increases at every addition of blocks.
10. Future-proofing through Cryptographic Agility
Last but not least, the most significant feature of Z-Text's quantum resistivity is the cryptographic agility. Because the system is built on a blockchain technology (BitcoinZ) which is changed through consensus with the community the cryptographic algorithms can be replaced as quantum threats become apparent. They are not tied to the same cryptographic algorithm forever. Additionally, as their history is shielded and their keys are kept in a self-pursuant manner, they're able to switch onto new quantum-resistant models without divulging their prior. The design ensures that communications are protected from threats to your current system, yet also for the ones to come.